At All Things Open 2021, the audience learned about best practices for supply chain security through a quiz game. This blog post walks through the quiz questions, answers, and options for prevention, and can serve as a beginner's guide for anyone who wants to protect their open source project from supply chain attacks. These recommendations follow the SLSA framework and OpenSSF Scorecards rubric, and many can be implemented automatically by using the Allstar project.
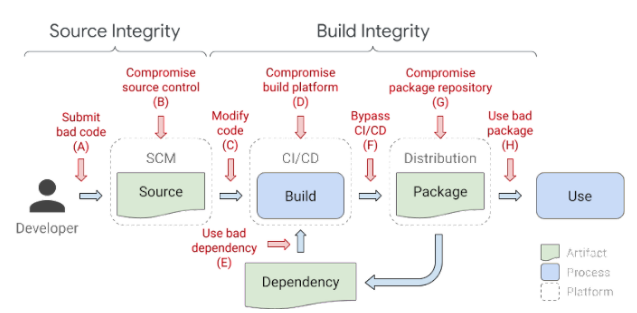
An example of a typical software supply chain and examples of attacks that can occur at every link in the chain.
- ANSWER: Use multi-factor auth (with a security key if possible)
- Use a shared account for core maintainers
- Make sure to write all your passwords in rot13
- Use an IP allowlist
Why and how: A malicious actor with access to a developer account can pretend to be a known contributor and submit bad code. Encourage contributors to use multi-factor authentication (MFA) not only for platforms where they send commits, but also for accounts associated with contributions, such as email. Where possible, security keys are the recommended form of MFA.
- ANSWER: Require all commits to be reviewed by someone who is not the commit author
- Auto-run tests on all commits
- Scan for the word ‘bitcoin’ in all commits
- Only accept commits from contributors who have accounts older than 1 year
Why and how: Self-merging (also known as a unilateral change) introduces two risks: 1) An attacker who has compromised a contributor’s account can inject malicious code directly into the project, or 2) A well-intentioned person can merge a commit that accidentally introduces a security risk. A second set of authenticated eyes can help avoid malicious submissions and accidental weaknesses. Set this up as an automated requirement if possible (such as using GitHub’s Branch Protection settings); tools like Allstar can help enforce this requirement. This corresponds to SLSA level 4.
- ANSWER: Use a secret manager tool
- Appoint a maintainer to control secrets access
- Store secrets as environment variables
- Store secrets in a separate repo
Why and how: The “defense in depth” security concept is about applying multiple, different layers of defense to protect systems and sensitive data, such as secrets*. A secret manager tool (like Secret Manager for GCP users, HashiCorp Vault, CyberArk Conjur, or Keywhiz) removes the need for hard-coding secrets in source code, provides centralization and audit capabilities, and introduces an authorization layer to prevent leaking secrets.
*When storing sensitive data in a CI system, ensure it is truly for CI/CD purposes, and not data that is better suited for a password or identity manager.
- ANSWER: Use access controls following the principle of least privilege
- Run integration tests on all pull requests/commits
- Mark all contributors as “Collaborators” through GitHub roles
- Run CI/CD systems locally
Why and how: Defaulting to “the least amount of access necessary” for your project repository protects your CI/CD system from both unintended access and abuse. While running tests is important, running tests on all commits/pull requests by default—before they’ve been reviewed—can lead to unintentional and malicious abuse of your CI/CD system’s compute resources.
- ANSWER: Define build definitions and configurations as code, eg build.yaml
- Make your builds run as quickly as possible so attackers have no time to compromise your code
- Only use LEGO brand components in your build system, accept no substitutes
- Delete build logs to avoid leaving clues for attackers
Why and how: Using a build script—a file that defines the build and its steps, like build.yaml—removes the need to manually run build steps, which could possibly introduce an accidental misconfiguration. It also reduces the opportunity for a malicious actor to tamper with the build or insert unreviewed changes. This corresponds to SLSA levels 1-4.
- ANSWER: Assess risk and transitive changes with tools like Scorecards and deps.dev
- Check for a little ‘lock’ icon next to the package url
- Only use dependencies that have a minimum of 1,000 GitHub stars
- Only use dependencies that have never changed maintainers
Why and how: There isn’t one definitive measure that can tell you a package is “good” or “bad;” every project has different security profiles and risk tolerances. Gathering information about a dependency, and what changes it might introduce transitively, will help you decide if a dependency is “safe” for your project. Tools like Open Source Insights (deps.dev) map first layer and transitive dependencies, while Scorecards gives packages a score for multiple risk assessment metrics, including use of security policies, MFA, and branch protection.
Once you determine what dependencies you’re using, running a vulnerability scanning tool such as Open Source Vulnerabilities regularly will help you stay up to date on the latest releases and patches. Many vulnerability scanning tools can also apply automatic upgrades.
- ANSWER: Use a build service that can generate authenticated provenance
- Check the last commit to be sure it’s from a trusted committer
- Use steganography to embed your project logo into the build
- Run conformance tests for each release
Why and how: Showing the origin and artifacts of a build (the build’s provenance) demonstrates to the user that the build has not been tampered with, and is the correct build. There are many components to provenance; one method to deliver these components is to use a build service that generates and authenticates the data needed to show provenance. This corresponds to SLSA levels 2-4.
- ANSWER: That artifacts have been cryptographically and verifiably signed
- That artifacts are not cursed (through being stolen from tombs)
- Timestamps: only use the most recent artifact created
- Official endorsement: look for the logo of a trusted brand or standards body
Why and how: Just as you should generate provenance and sign builds for your projects (SLSA levels 2-4), you should also look for the same verification when using artifacts from others. Logos and other brand-based forms of endorsement can be falsified and are used by typosquatters to fake legitimacy; look for tamper-proof verification like signatures. For example, Sigstore helps OSS projects sign their builds, and validate the builds of others.
Improving your project’s security is a continuous journey. Some of these recommendations may not be feasible for your project today, but every step you can take to increase your project’s security is a step in the right direction.
Resources for open source project security:
- SLSA: A framework for levels of supply chain security
- Scorecards: A measurement of security best practices use
- Allstar: A GitHub app for enforcing security best practices
- Open Source Insights: A searchable visualization of open source project dependencies
- OSV: A vulnerability database and automation infrastructure for open source